- Newest
- Most viewed

How to Choose the Right Office Pod for Your Backyard
How to choose between the WorkPod Core, Pro, and Versatile - climate, square footage, outlet count, and which one fits your use case. Verified specs and pricing.
Workplace Inspiration | May 25, 2026 2,740 views

The Engineering Behind an Office Chair for Neck Pain
Smart Products | May 22, 2026 9,989 views
.webp)
Best Petite Office Chairs for Short People 2026 - Tested
Smart Products | May 14, 2026 36,264 views
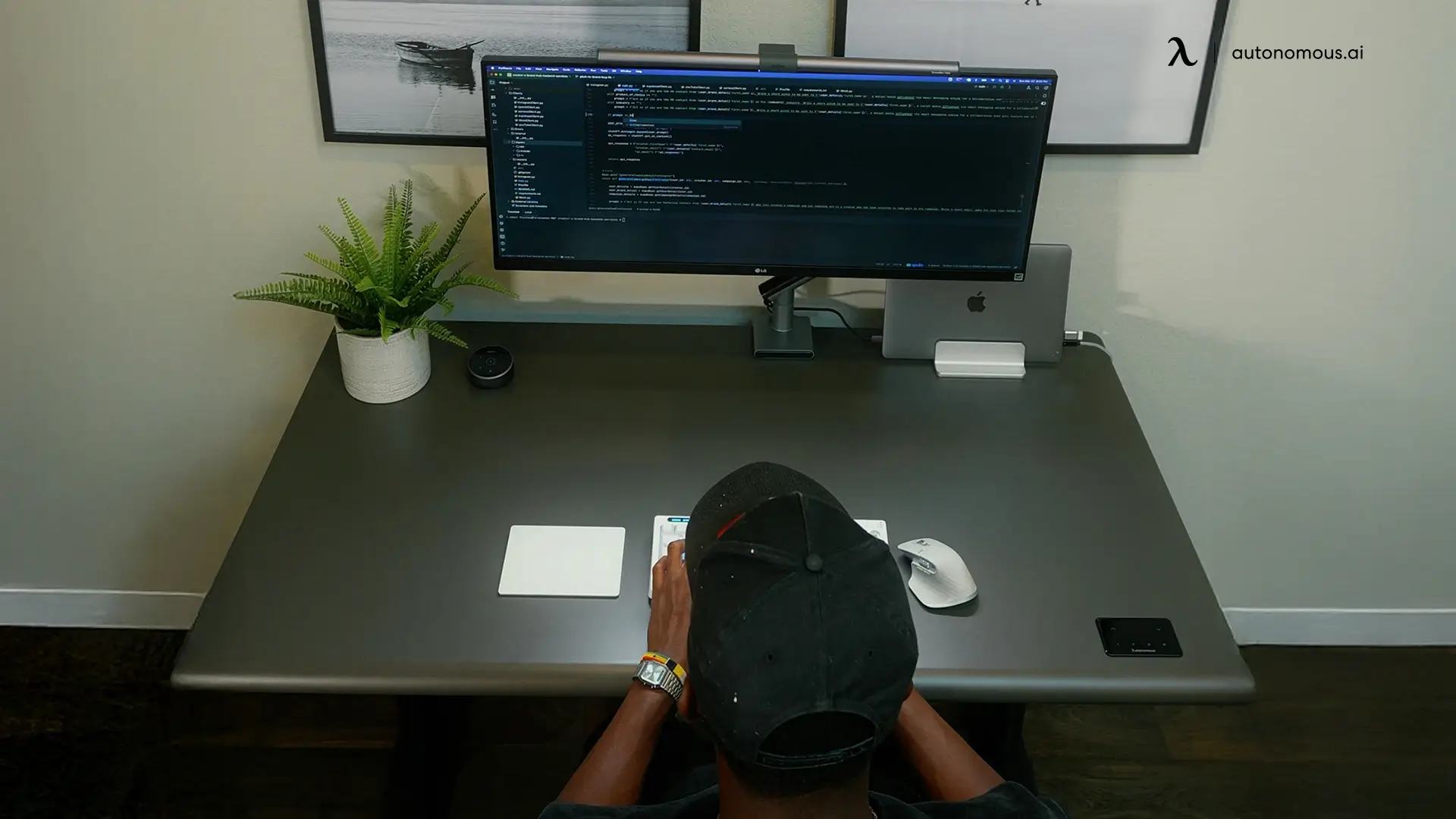
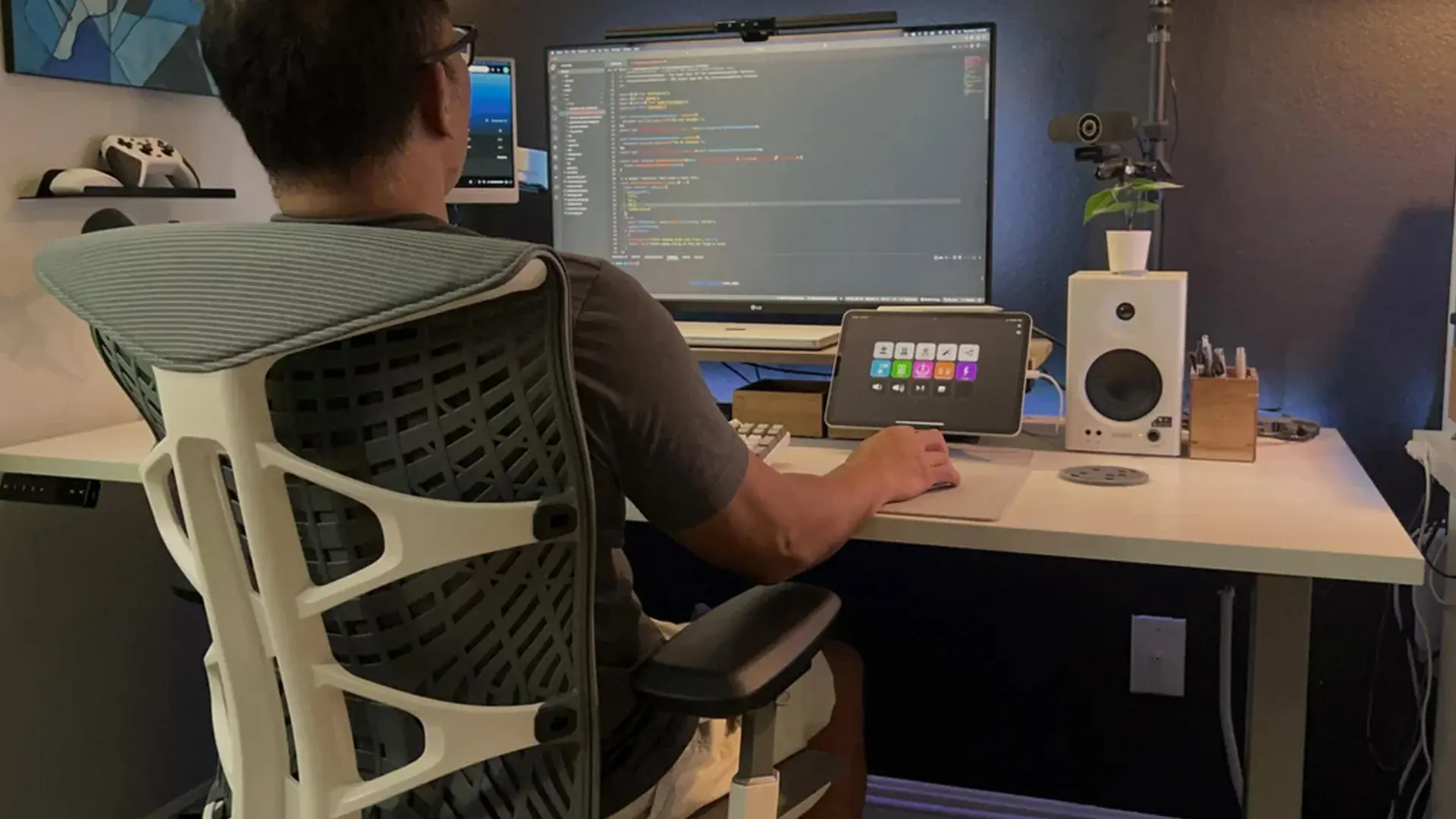
Real Developer Desk Setup for Multi-Agent Workflows
Workplace Inspiration | May 12, 2026 138,197 views

Autonomous Desk Pro vs Desk 2 - The Quieter Desk Lifts 80 lb More
Smart Products | May 11, 2026 3,838 views
The Best 8-Hour Office Chairs, Tested Hour by Hour
Smart Products | May 11, 2026 27,028 views

The ErgoChair Ultra 2 Fit for Petite Women - by an Engineer
Smart Products | May 8, 2026 12,088 views

A Guide to Standing Desk Replacement Parts
Smart Products | May 8, 2026 8,408 views

How to Size an Office Chair for Real Work
Smart Products | May 8, 2026 42,039 views

Autonomous ErgoChair Pro vs ErgoChair Ultra 2
Smart Products | May 6, 2026 4,089 views

The Office Chairs for Core Strength I Tested
Smart Products | May 5, 2026 9,051 views

Small Backyard Office Sheds Worth Buying in 2026
Workplace Inspiration | May 1, 2026 10,249 views